One day, a journalist named Alice receives a sensitive tip from Bob. She hesitates to contact him, as email feels too risky. Finally, she decides to use a messaging app called Signal. She sends the message, it disappears within minutes, then she sleeps without knowing that Signal can’t even read what she has sent. But how is that possible? How can an app deliver a message it can’t even see? In this blog post, I will try my best to answer this question.
What is Encryption?
Before discussing how the Signal Protocol works and how messaging apps keep your conversations private, we should understand encryption and its types.
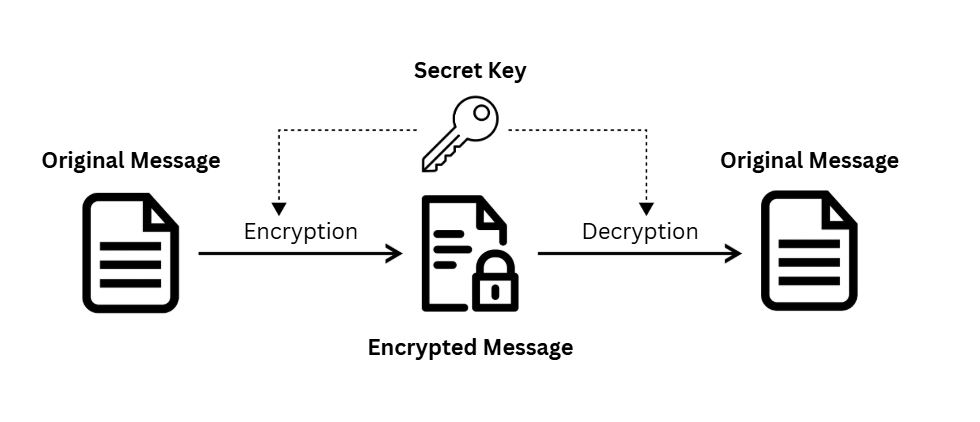
Encryption is a way of transforming information so that only authorized parties can understand it. In technical terms, it’s converting human-readable plaintext to incomprehensible text, also known as ciphertext, by using a cryptographic key so that the data appears random.
Symmetric Encryption
This type of encryption uses the same key to encrypt and decrypt the message on both sides. Think of it this way: you want to send your friend a message, so you put it in a box and lock it with a key. When your friend gets the box, he uses the same key to open it and read your message.
Asymmetric Encryption
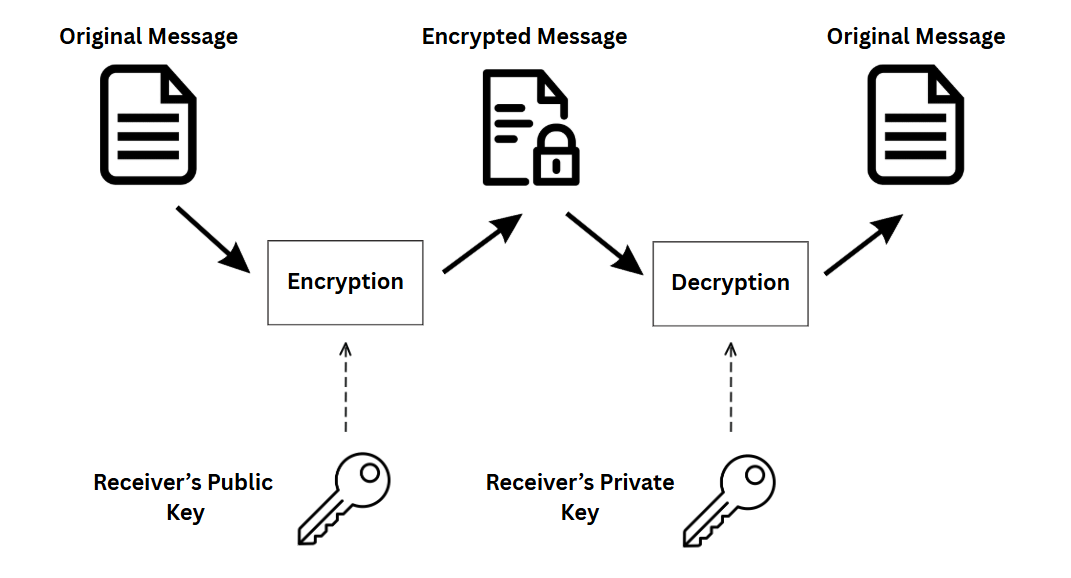
This type of encryption works differently as it uses two keys instead of one: a public and a private key.
- Public keys are like mailboxes — anyone can drop a message into them. For example, if Alice wants to send Bob a message, she uses Bob’s public key to encrypt it.
- Private keys are the only keys that open the mailbox, and only Bob should have them. When he gets Alice’s message, he uses the private key to decrypt it and read what’s inside.
End-to-End Encryption (E2EE)
End-to-end encryption (E2EE) is a way of implementing secure communication to prevent third parties from accessing the data transferred by encrypting it beforehand. When you chat on Signal, your conversations are always protected this way — preventing the data from being read or secretly modified, not even by the messaging app itself.
Meet the Building Blocks: How Signal Protocol Works
X3DH: The Key Exchange That Starts It All
Before jumping to X3DH, let’s look at the classic Diffie-Hellman key exchange. Diffie–Hellman (DH) key exchange is a method to securely generate a cryptographic key over a public channel.
Understanding Diffie-Hellman Key Exchange
Despite the name suggesting that a key exchange happens somewhere, we don’t actually exchange the keys themselves — if we did, it would be out in public and anyone could grab it. So what happens is we exchange some public variables and use them to independently generate the same secret key on each side.
Let’s break it down using a color-mixing analogy. The process starts with Alice and Bob agreeing on a shared starting color — let’s say yellow. This color is public. Then each person picks a secret color:
- Alice chooses red
- Bob chooses cyan
They mix their secret color with the shared yellow:
- Alice mixes yellow + red → gets orange-tan
- Bob mixes yellow + cyan → gets light-blue
Now they exchange their mixed colors publicly. Then the magic happens:
- Alice takes Bob’s mixed color (light blue) and mixes it with her secret red
- Bob takes Alice’s mixed color (orange-tan) and mixes it with his secret cyan
Both end up with the same final color. A third party watching only knows the common color and the first mixed colors — they can’t figure out the final secret because they don’t know the private colors Alice and Bob started with.
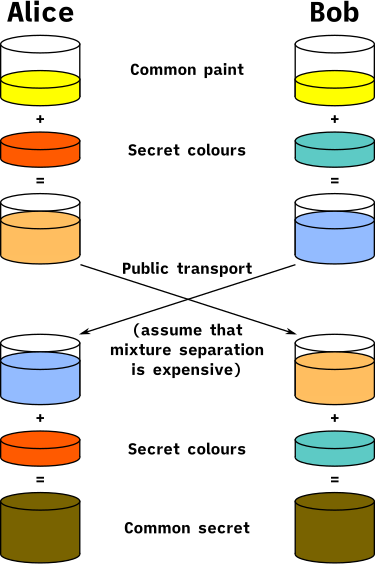
In real cryptography, we don’t use colors — we use big numbers. Figuring out the final secret without knowing the private part would take even modern supercomputers thousands of years.
What’s the Catch?
Diffie-Hellman works only if both people are online at the same time to exchange keys — which isn’t the case in most messaging apps. So how can we make secure key exchange work asynchronously?
Enter X3DH: Asynchronous and Secure
X3DH (Extended Triple Diffie-Hellman) is designed for asynchronous settings where one user is offline but has published information to the server. This allows Alice to start an encrypted conversation with Bob even if Bob is offline.
The X3DH protocol involves five public keys:
- Alice has:
- Identity key (
IK_A): A long-term public key that identifies Alice. - Ephemeral Key (
EK_A): A temporary key used only for this session.
- Identity key (
- Bob has:
- Identity key (
IK_B): A long-term public key that identifies Bob. - Signed preKey (
SPK_B): A medium-term public key signed by Bob’s identity key. - One-time prekey (
OPK_B): A single-use public key for the initial session (optional).
- Identity key (
These keys are used in three phases:
- Bob uploads his three keys to a server.
- Alice downloads these keys and verifies the signature on
SPK_B. - Once verified, Alice uses them to send the initial message.
Double Ratchet: Keeping Secrets Fresh
Double Ratchet is a key management algorithm used to manage the ongoing renewal of short-lived session keys.
You might wonder: if Alice and Bob created a shared secret, why do we need more key changes later? The short answer is: secrets get old fast, and in private messaging, even a single mistake can leak your past or future messages.
1. The Symmetric (KDF) Ratchet
This ratchet creates a new key every time you send or receive a message. It uses a Key Derivation Function (KDF) — a math function that takes one key and turns it into a new one in a predictable but secure manner:
- You send a message, then use the current key in KDF to derive a new key.
- You throw away the old key and use the new one for the next message.
- This repeats every message.
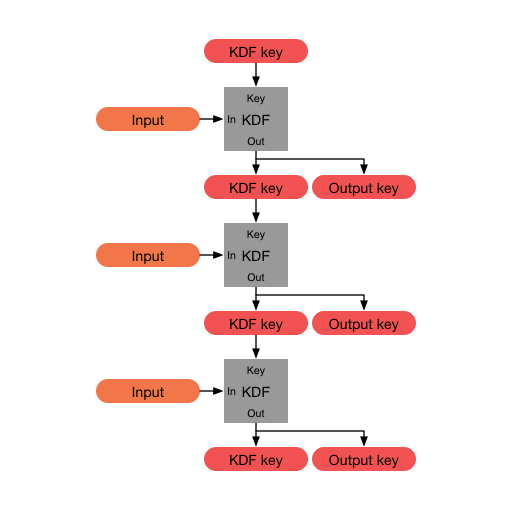
This means if someone steals your current key, they can’t go backward to unlock past messages — this is called forward secrecy.
But here’s the catch: if someone gets your current key, they can follow the chain forward to read all future messages, since each key is built from the last one. That’s where the second ratchet steps in.
2. The Diffie-Hellman (DH) Ratchet
This ratchet breaks the forward chain by exchanging public keys to create a new root secret — one that no one watching the previous chain could guess. This resets everything, so if someone got your keys before, new messages are built on a completely different secret path. This gives you post-compromise security: the ability to recover from an attack.
Bonus: What About Post-Quantum?
Quantum computers could one day break traditional encryption schemes. Algorithms like RSA and classic Diffie-Hellman would be vulnerable to quantum attacks via something called Shor’s algorithm.
Post-quantum cryptography (PQC) is a field concerned with developing algorithms that can’t be broken by quantum attacks. Researchers are already working on post-quantum versions of X3DH and Double Ratchet, combining them with quantum-resistant algorithms like Kyber or FrodoKEM.
Some experimental messaging protocols — like PQXDH by Signal — aim to upgrade the key exchange while keeping everything else the same. So for now, Signal is secure. But in the future, expect cryptographic upgrades to keep your messages safe even from quantum computers.
Wrap-Up
By now, you’ve gone beyond the surface level of Signal and explored how their private messaging protocol works and why it’s trusted. You’ve learned:
- How end-to-end encryption keeps messages private.
- Why features like forward secrecy and the Double Ratchet matter.
- That Signal isn’t just an app — it’s a protocol designed with security and privacy as its foundation.
So the next time someone tells you end-to-end encryption is just a buzzword, you’ll know better.